BGP and BGPSec...you really should care about this
The future open-ness of the Internet is at stake. The Secure Inter-Domain Routing Working Group is working on a replacement for the BGP protocol called BGPSEC. This is one of those little-known technologies that affects you every day. You really don't want one group with consolidated power over the Internet.
What is BGP?
First, you need to know what BGP is. Border Gateway Protocol is used to make core routing decisions on the Internet. ISPs must use BGP to establish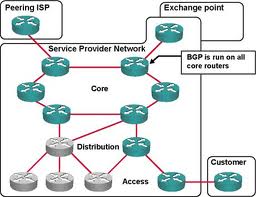 routing between each other, making it one of the most important protocols that makes the Internet work. An autonomous network uses BGP to determine which systems are neighboring it and what their IP "prefix" is. It "discovers" the IP networks and peers around it. Every 30 seconds a BGP peer will send a keep-alive message to its neighbors to maintain its status. On very large networks the route tables can grow unwieldy. Over the years ISPs cooperated and implemented solutions like CIDR to tame the growth. This also added stability because if a major internet backbone went down the whole internet "service" would become unreliable until the routing tables stability. Note that there was no legal mandate to do this, ISPs simply cooperated because it was the right thing to do. The free market at work basically.
routing between each other, making it one of the most important protocols that makes the Internet work. An autonomous network uses BGP to determine which systems are neighboring it and what their IP "prefix" is. It "discovers" the IP networks and peers around it. Every 30 seconds a BGP peer will send a keep-alive message to its neighbors to maintain its status. On very large networks the route tables can grow unwieldy. Over the years ISPs cooperated and implemented solutions like CIDR to tame the growth. This also added stability because if a major internet backbone went down the whole internet "service" would become unreliable until the routing tables stability. Note that there was no legal mandate to do this, ISPs simply cooperated because it was the right thing to do. The free market at work basically.
There are other problems such as load-balancing and IP hijacking. The latter can occur due to DoS attacks, attempts at censorship, or programming errors. As they say, it happens. The heart of the "problem" is that routing information exchanged over the BGP protocol is not verifiable.
What is BGPSEC?
BGPSEC is only one of many possible solutions to the hijacking problem. BGPSEC creates a kind of PKI infrastructure to verify the data. It centralizes
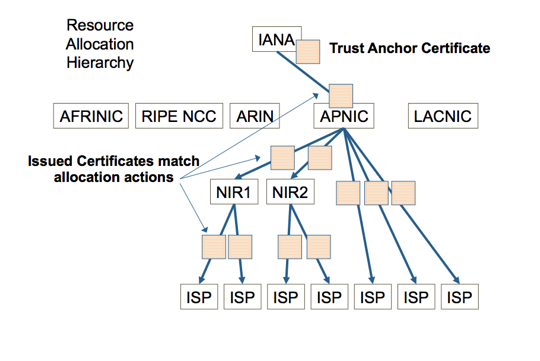 security and makes it mandatory. It uses a government-like body with total dominance over the underlying routing protocol of the Internet. IANA is the body that currently doles out IP addresses and according to the proposal it will be responsible for the PKI infrastructure as well. IANA is basically an arm of the US Dept of State.
security and makes it mandatory. It uses a government-like body with total dominance over the underlying routing protocol of the Internet. IANA is the body that currently doles out IP addresses and according to the proposal it will be responsible for the PKI infrastructure as well. IANA is basically an arm of the US Dept of State.
The proposed PKI infrastructure has another nefarious side-effect...it has the ability to sieze a range of IP addresses and spoof them, or even a SINGLE IP address. Hopefully you can see where I'm going with this. The government can shut down a single host or even an entire country if it doesn't like its content. All of that could be done without a warrant or due process of law. That is disconcerting.
addresses and spoof them, or even a SINGLE IP address. Hopefully you can see where I'm going with this. The government can shut down a single host or even an entire country if it doesn't like its content. All of that could be done without a warrant or due process of law. That is disconcerting.
If BGPSEC can spoof any IP address then it can also spy on any host. And using man-in-the-middle attacks it could even decrypt your traffic if it wanted to.
Alternatives
We can distribute security resources without creating a hierarchy and centralization. This model is proven to work. This is how P2P networks work, and they work very well. As much as certain groups (RIAA) would love to shut them down, they can't. They are too open and distributed. Same with Bitcoin.
Verisign has come out and said that a consortium of private enterprises should handle this PKI infrastructure and share in the responsibilities. This is how current PKI certificates work. And it works very well. Verisign both cooperates and competes with many other similar firms such as Thawte.
Summary and Conclusions
The Internet was meant to be free. Seriously, that is NOT hyperbole. We all know how the original architects of the Internet wanted to build openness and redundancy into the system. If a single host went down it didn't take the whole network down. BGPSEC reverses those fundamental decisions. Now one agency will control so much of the Internet that essentially they could shut it down.
Why do I care about this? Why should "data" people care about this? BGPSEC is actually a pretty cool solution to a given problem. But it isn't the right solution. I outlined alternatives that are "right." Engineers and architects are smart people and we love nifty solutions. But we must never forget the ethics of solutions we propose. Ethically I have problems with BGPSEC. It's only a matter of time until the government has a "problem" with the Internet and a contractor builds a tool to solve that problem using BGPSEC infrastructure. It's at that point where a harmless piece of software has the ability to enslave humanity.
solution. I outlined alternatives that are "right." Engineers and architects are smart people and we love nifty solutions. But we must never forget the ethics of solutions we propose. Ethically I have problems with BGPSEC. It's only a matter of time until the government has a "problem" with the Internet and a contractor builds a tool to solve that problem using BGPSEC infrastructure. It's at that point where a harmless piece of software has the ability to enslave humanity.
Dave Wentzel CONTENT
other
